Although Builder clearly is The Future as GNOME IDE, I still all my coding in Emacs, mostly because I have been using it for such a long time that my brain is to all the shortcuts and workflows. But Emacs can be a good IDE too. The most obvious everyday features that I want from an IDE are good source code navigation and active assistance while editing. In the first category are tasks like jumping to symbol's definition, find all callers of a function and such things. For editing, auto-completion, immediate warnings and error reporting, semantic-aware re-factoring are a must. Specifically for GNOME related development, I need all this to also work with JHBuild.
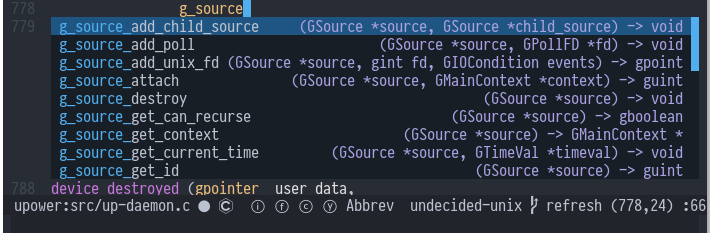
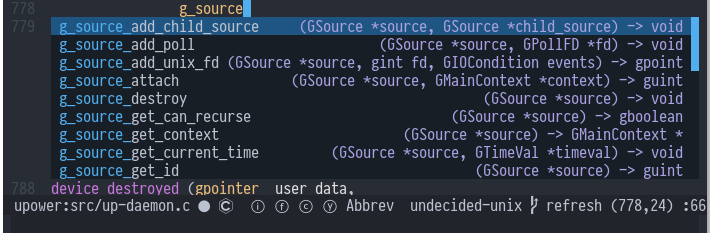
Auto-completion via irony-mode
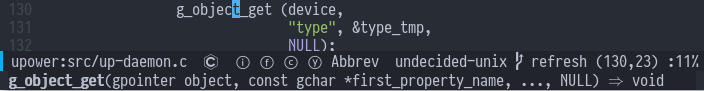
Emacs can do all these with a combination of various packages: RTags indexes C/C++ source code and provides all sorts of functionality on top of that, like follow-symbol, find-references, rename-symbol and even fix obvious errors for you (via clang's "Fix-It Hints"). Auto-completion and "online" diagnostics are currently handled via Irony-mode (via company-irony and company-flycheck); RTags could do both too, I use irony-mode mostly for historic reasons and it works quite well. Additionally, irony-mode also has integration with eldoc-mode, that will show function signatures in the mode-line.
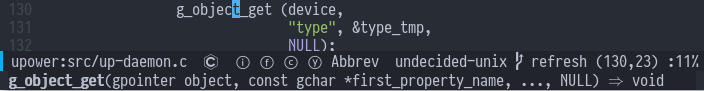
Eldoc integration
compile database compiler wrapper
Both of these packages use (lib)clang internally, which in turn needs to know the right compile flags for all source files. CMake and other modern build system can generate a compile_commands.json file that contains that information. For automake/autoconf based projects a wrapper around gcc can in theory be used to generate the file. But for JHBuild that approach is not working, because the build directory is not the source directory, so the wrapper generates the files in the wrong place. To work around this I wrote a special gcc wrapper and small set of tools, called cdcc (for compile database cc). The cdcc-gcc wrapper will store the compile flags in a sqlite database and the cdcc-gen command can then be called with a path to the source directory to generate the corresponding compile_commands.json. The easy way to use cdcc with JHBuild is to put the following in your ~/.config/jhbuildrc (this includes a fallback if it is not installed):
if spawn.find_executable('cdcc-gcc') is not None:
os.environ['CC'] = 'cdcc-gcc'
os.environ['CXX'] = 'cdcc-g++'
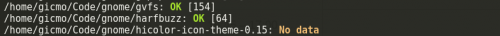
After the build is done, the compile_commands.json for each module can then be generated with cdcc-gen * in the JHBuild checkout root. The Emacs package cmake-ide is used to automatically set up RTags and friends with the correct settings, if it detects the compile_commands.json file.
Installation
RPMs for Fedora of RTags and cdcc can be found in my copr. The rdm server for RTags can easily be started via systemd socket activation, instructions are here. I install the irony-server binary locally in my ~/.emacs.d folder via a custom script.
I load all Emacs packages with use-package, you can look at my init.el for details.